Penetration testing, often called pen testing, is a cornerstone of modern cybersecurity. It involves simulating attacks on systems, networks, or applications to identify vulnerabilities before malicious actors exploit them. This proactive approach helps organizations strengthen their defenses and mitigate potential risks.
From open-source solutions to advanced commercial platforms, the right software can enhance efficiency, accuracy, and the depth of insights gained during a pen test.
Why Is Software Crucial for Penetration Testing?
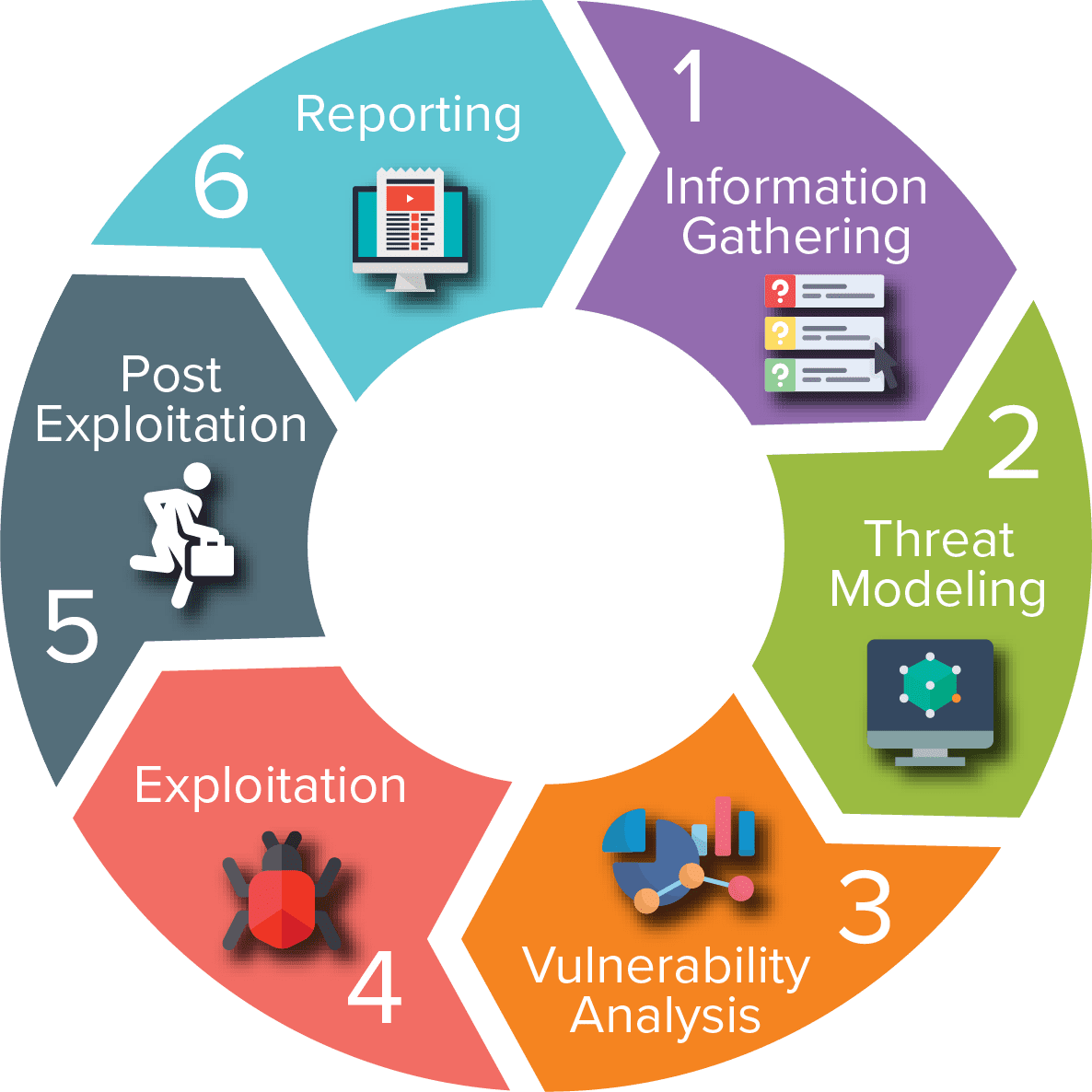
Penetration testing is a multi-step process, typically involving planning, reconnaissance, vulnerability assessment, exploitation, and reporting. Each stage demands precision, speed, and often a wide array of technical capabilities. This is where specialized software plays a pivotal role.
Enhancing Efficiency and Accuracy
- Automation: Tools like Nessus and Burp Suite automate repetitive tasks such as vulnerability scanning and web application testing, saving testers hours of manual work.
- Scalability: Software handles large-scale tests across vast networks, something nearly impossible to achieve manually.
- Minimized Human Error: Sophisticated tools ensure consistency and precision, reducing the chances of oversight.
Streamlining Reporting
Comprehensive reporting tools integrated into platforms like Qualys or Cobalt Strike help testers document findings clearly and professionally. This aids stakeholders in understanding risks and prioritizing remediation.
Adapting to Evolving Threats
Cybersecurity is ever-changing. Tools like Metasploit and Aircrack-ng are regularly updated to address new attack vectors, ensuring penetration testers stay ahead of the curve.
Real-World Impact
A 2022 study by the Ponemon Institute revealed that organizations using automated pen testing tools reduced the average time to identify and mitigate vulnerabilities by 47%. This showcases how vital the right software is in today’s threat landscape.

Categories of Software Used in Penetration Testing
Penetration testing software spans various categories, each tailored to a specific stage of the testing process. From gathering information about a target to exploiting vulnerabilities and analyzing results, these tools form the backbone of a penetration tester’s arsenal. Below, we’ll explore the most commonly used categories and highlight popular tools in each.
Reconnaissance and Information Gathering Tools
Reconnaissance is the first step in penetration testing, involving the collection of information about the target system or network. The goal is to identify entry points, technologies in use, and potential weaknesses.
- Nmap (Network Mapper): An essential tool for network discovery and port scanning, Nmap helps testers map the structure of a network, revealing open ports and services. For example, Nmap’s scripting engine can detect outdated software, a common vulnerability.
- Maltego: Ideal for OSINT (Open-Source Intelligence), Maltego visualizes relationships between people, domains, and networks. This is particularly useful in social engineering and phishing scenarios.
- Shodan: Known as the “search engine for the Internet of Things (IoT),” Shodan identifies publicly exposed devices like webcams, routers, and industrial systems.
Case Study: A penetration test on a financial institution used Shodan to identify misconfigured IoT devices, revealing an insecure entry point that could be exploited remotely.
Vulnerability Scanners
These tools automate the detection of vulnerabilities in systems, applications, and networks, providing a roadmap for further exploitation.
- Nessus: Widely regarded for its comprehensive scanning capabilities, Nessus identifies vulnerabilities, misconfigurations, and compliance issues.
- OpenVAS (Open Vulnerability Assessment System): A powerful open-source scanner that excels in detecting a wide array of vulnerabilities.
- Qualys: This enterprise-grade scanner integrates with cloud platforms, making it a preferred choice for organizations with hybrid infrastructures.
Pro Tip: Regular vulnerability scans combined with manual validation by penetration testers ensure both depth and accuracy in assessments.
Exploitation Tools
Exploitation tools are used to simulate attacks on identified vulnerabilities. These tools allow testers to validate the impact of vulnerabilities by demonstrating potential breaches.
- Metasploit Framework: A highly versatile exploitation framework, Metasploit provides an extensive library of exploits and payloads. It also supports post-exploitation tasks like privilege escalation.
- SQLmap: This tool automates the detection and exploitation of SQL injection flaws, a common vulnerability in web applications.
- Exploit-db: While not software, this repository of publicly disclosed exploits is a vital resource for penetration testers.
Example in Action: Using SQLmap, a tester successfully accessed sensitive user data from a poorly coded web application, illustrating the risks of SQL injection vulnerabilities.
Password Cracking Tools
Testing password strength is essential to identify weak or reused passwords that attackers can exploit.
- Hashcat: Known for its speed and efficiency, Hashcat supports a wide range of hashing algorithms, making it ideal for brute-force attacks.
- John the Ripper: This open-source tool excels in detecting weak passwords, particularly in UNIX environments.
- Hydra: Specialized in network authentication cracking, Hydra targets protocols like FTP, SSH, and HTTP.
Stat to Consider: According to Verizon’s 2023 Data Breach Investigations Report, 81% of breaches involved weak or stolen passwords, emphasizing the need for robust password testing.
Wireless Network Testing Tools
Wireless networks are frequent targets for attackers, making their security a critical focus during penetration tests.
- Aircrack-ng: A suite of tools for assessing Wi-Fi network security, including packet capture and decryption.
- Wireshark: While primarily a network protocol analyzer, Wireshark aids in identifying anomalies in wireless traffic.
- Kismet: Useful for detecting hidden or rogue wireless networks.
Scenario: During a pentest of a corporate network, Aircrack-ng exposed weak WPA2 encryption, leading to a complete overhaul of the company’s wireless security policies.
Web Application Testing Tools
Web applications often harbor vulnerabilities due to their complexity and public accessibility. Dedicated tools focus on identifying and exploiting these weaknesses.
- Burp Suite: A comprehensive platform for web app security testing, including features like proxying, spidering, and vulnerability scanning.
- OWASP ZAP (Zed Attack Proxy): An open-source alternative to Burp Suite, ZAP is excellent for finding common web vulnerabilities like XSS and CSRF.
- Acunetix: A commercial tool specializing in automated scans for web app vulnerabilities and compliance issues.
Real-World Use: Pen testers used Burp Suite to discover a persistent XSS vulnerability in an e-commerce site, potentially allowing attackers to steal customers’ login credentials.
Social Engineering Tools
Social engineering tools simulate phishing attacks or other human-centric exploits, revealing non-technical vulnerabilities.
- SET (Social-Engineer Toolkit): Designed for spear phishing and other social engineering attacks.
- Gophish: A platform for creating and managing phishing campaigns.
Nearly 98% of cyberattacks involve some form of social engineering. Using tools like SET, penetration testers can simulate these attacks to educate and prepare users.
Post-Exploitation Tools
Post-exploitation focuses on maintaining access to compromised systems and gathering additional intelligence.
- Empire: A post-exploitation framework for Windows and Linux environments.
- Cobalt Strike: This tool facilitates covert operations, such as lateral movement and persistence.
Highlight: These tools emphasize the potential long-term impacts of a breach, helping organizations understand the depth of their vulnerabilities.

Free vs Paid Penetration Testing Software
Choosing between free and paid penetration testing software depends on factors like project requirements, budget, and the desired level of sophistication. Each option has its strengths and limitations, and understanding these can help testers make informed decisions.
Benefits of Free/Open Source Software
Free and open-source tools are highly popular among penetration testers, especially those just starting in the field or working with limited budgets. These tools often have strong community support and cover a wide range of testing needs.
- Accessibility: Free tools like Kali Linux and OWASP ZAP provide robust features without the need for financial investment.
- Customizability: Open-source tools allow testers to modify and adapt software to suit specific needs.
- Community Support: Active developer and user communities ensure regular updates and provide a wealth of tutorials, forums, and documentation.
Popular Free Tools:
| Tool | Category | Key Features |
|---|---|---|
| Kali Linux | Comprehensive OS | Pre-installed with 600+ pen testing tools. |
| Wireshark | Network Analysis | Detailed protocol inspection and traffic capture. |
| Metasploit | Exploitation Framework | Library of exploits and payloads. |
Example: A freelance penetration tester used the free capabilities of Kali Linux and Wireshark to secure a small business’s network, showcasing the power of free tools for small-scale projects.
Advantages of Paid Software
While free tools are powerful, paid software often includes advanced features, better integration options, and superior support, making them a preferred choice for enterprise-level penetration testing.
- Advanced Features: Paid tools like Burp Suite Professional and Nessus Professional offer enhanced capabilities, such as automated scanning, advanced analytics, and customization options.
- Professional Support: Dedicated customer service ensures timely assistance for troubleshooting and updates.
- Compliance and Reporting: Paid tools typically include robust reporting features that meet industry compliance standards like PCI-DSS, HIPAA, and GDPR.
Popular Paid Tools:
| Tool | Cost Approximation | Features |
|---|---|---|
| Burp Suite Professional | $399/year | Advanced vulnerability scanning for web apps. |
| Nessus Professional | $2,990/year | Enterprise-grade vulnerability assessment tools. |
| Cobalt Strike | $5,900/year | Post-exploitation and red team operations. |
Use Case: A Fortune 500 company implemented Cobalt Strike for red team simulations, which revealed weaknesses in its incident response process, leading to significant improvements in security protocols.
Key Considerations When Choosing Free or Paid Tools
| Factor | Free Tools | Paid Tools |
|---|---|---|
| Budget | Ideal for startups and individuals. | Suited for large organizations. |
| Complexity of Needs | Best for simple or moderate tasks. | Handles complex enterprise environments. |
| Compliance Needs | Limited built-in reporting. | Tailored compliance reports. |
| Learning Curve | May require more manual configuration. | User-friendly, with professional support. |
The Hybrid Approach: Combining Free and Paid Tools
Many penetration testers combine free and paid tools to maximize their efficiency and minimize costs. For instance:
- Reconnaissance: Using free tools like Nmap and Shodan for initial data gathering.
- Exploitation: Leveraging Metasploit (free) alongside Burp Suite Professional (paid).
- Reporting: Relying on Nessus Professional for enterprise-grade reporting.
Expert Tip: A hybrid strategy ensures cost-effective testing while maintaining access to high-quality features when needed.
Platforms and Operating Systems for Penetration Testing Software
The choice of platform or operating system plays a crucial role in penetration testing. Different tools have varying compatibility and performance, and selecting the right environment can significantly enhance efficiency and effectiveness. Below, we explore the most commonly used platforms and operating systems in penetration testing.
Kali Linux as a Standard Platform
Kali Linux is the most widely recognized operating system for penetration testers, often referred to as the “gold standard” for ethical hacking.
- Pre-Installed Tools: Kali Linux comes with over 600 penetration testing tools, including Nmap, Metasploit, and Wireshark, eliminating the need for extensive manual installations.
- Ease of Use: Designed specifically for cybersecurity professionals, Kali Linux features an intuitive interface and robust documentation.
- Portability: The ability to run Kali Linux as a live boot system or on a virtual machine makes it incredibly versatile.
Why Professionals Prefer Kali:
- Regular Updates: The team behind Kali Linux ensures its tools and repositories remain up-to-date.
- Community Support: Extensive online resources and forums provide quick solutions to problems.
Case Study: A penetration tester used Kali Linux on a live USB during an on-site test, accessing all necessary tools without installing anything on the client’s hardware, ensuring minimal footprint.
Alternatives to Kali Linux
While Kali Linux is the dominant choice, other operating systems offer unique advantages, catering to different needs and preferences.
- Parrot OS:
- A lightweight alternative to Kali Linux with similar penetration testing tools.
- Emphasizes privacy, featuring tools like Anonsurf for anonymous browsing.
- BlackArch Linux:
- Built for advanced users, BlackArch includes over 2,700 hacking tools.
- Its steep learning curve makes it more suited for seasoned penetration testers.
- Windows Subsystem for Linux (WSL):
- Allows users to run Linux distributions (like Kali or Parrot OS) directly on Windows.
- Ideal for testers who need to operate in a Windows environment while leveraging Linux tools.
Comparison of Platforms:
| Platform | Key Features | Best For |
|---|---|---|
| Kali Linux | Comprehensive toolkit, easy to use | Beginners and professionals |
| Parrot OS | Lightweight, privacy-focused | Resource-limited systems |
| BlackArch | Massive tool repository, complex | Experienced testers |
| WSL | Linux on Windows integration | Mixed Windows/Linux environments |
Cross-Platform Tools
Many penetration testing tools are designed to work seamlessly across multiple platforms, offering flexibility regardless of the operating system.
- Wireshark: Available for Windows, Linux, and macOS, Wireshark is a go-to tool for network analysis.
- Burp Suite: Compatible with major operating systems, ensuring smooth operation across diverse environments.
- Metasploit Framework: While primarily Linux-focused, Metasploit also runs on Windows and macOS, making it highly versatile.
Expert Tip: Using cross-platform tools ensures that testers can adapt to different client environments without compatibility issues.
Virtualized Environments for Penetration Testing
Virtualization provides a safe and isolated environment for testing, especially useful for beginners and training purposes.
- Virtual Machines (VMs): Platforms like VMware and VirtualBox allow testers to create isolated environments for running penetration testing OSes like Kali Linux.
- Docker: A lightweight alternative to VMs, Docker containers can host individual tools or small setups, enabling faster deployment.
Example Setup: A penetration tester sets up a virtualized lab using VirtualBox with three VMs:
- A Kali Linux attacker machine.
- A Windows server with vulnerable software for exploitation practice.
- A Linux web server for web application testing.
This approach ensures safety and avoids affecting production environments.