Penetration testing, often referred to as pen testing or ethical hacking, is the practice of assessing the security of an organization’s systems, networks, and applications by simulating a cyberattack. The goal of penetration testing is to identify vulnerabilities that hackers could exploit, thus enabling businesses to fix these issues before they are targeted in real cyberattacks.
Penetration testers (also called ethical hackers, white-hat hackers, or security consultants) use a combination of tools, techniques, and their own expertise to identify weaknesses in a company’s IT infrastructure. These tests can be carried out on various systems, including websites, networks, web applications, and even physical security.

Penetration testing is an essential practice for any organization that wants to strengthen its cybersecurity defenses and ensure that it is not vulnerable to data breaches, ransomware attacks, or other types of cybercrime.
Why Are Penetration Testers Important?
Penetration testers play a critical role in the cybersecurity landscape. Here’s why they are so important:
- Identifying Weaknesses Before Hackers Do: Pen testers proactively look for vulnerabilities in systems, helping organizations close the gaps before malicious hackers can exploit them.
- Preventing Financial Losses: The cost of a successful cyberattack can be enormous—ranging from lost data to expensive fines for non-compliance with data protection regulations (such as GDPR). Penetration testing helps prevent these losses.
- Reputation Protection: Data breaches and other security incidents can significantly damage a company’s reputation. Penetration testing is a way to demonstrate a company’s commitment to cybersecurity.
- Compliance with Legal and Industry Standards: Many industries require regular penetration tests to meet compliance regulations. For instance, healthcare, finance, and e-commerce industries must adhere to strict standards regarding data security.
A penetration tester (also known as an ethical hacker, security consultant, or white-hat hacker) is a cybersecurity professional who simulates cyberattacks to identify vulnerabilities in a company’s IT infrastructure. Their role is to uncover weaknesses before malicious hackers can exploit them. By testing systems, networks, web applications, and even physical security, penetration testers help organizations protect their data and assets from cyber threats.
Unlike malicious hackers who aim to cause damage or steal sensitive information, penetration testers work within legal and ethical boundaries, with the permission of the company being tested. They use their skills to find and exploit weaknesses, but their ultimate goal is to provide solutions to strengthen the security posture of the organization.
Key Responsibilities of a Penetration Tester
The responsibilities of penetration testers can vary depending on the specific test, but generally, their tasks include the following:
- Identifying Vulnerabilities: Penetration testers search for security gaps in the systems they are testing. This could include anything from outdated software versions to misconfigured firewalls or unprotected endpoints.
- Simulating Real-World Attacks: Once they identify vulnerabilities, pen testers simulate how an attacker might exploit these weaknesses. This includes using various hacking techniques (e.g., SQL injection, social engineering, privilege escalation) to gain unauthorized access to systems or data.
- Reporting Findings: After the test is complete, penetration testers provide detailed reports to their clients. These reports typically highlight the vulnerabilities found, the potential risks, and the steps needed to resolve them.
- Providing Recommendations: Penetration testers don’t just identify problems—they also help organizations improve their defenses. Their reports include recommendations for addressing vulnerabilities, patching security flaws, and improving overall security posture.
- Collaboration with Other Teams: Penetration testers often work closely with IT teams, network security professionals, and developers to help implement solutions for the vulnerabilities they’ve found. They may even help prioritize which vulnerabilities should be patched first based on risk and impact.
Difference Between Penetration Testing and Other Security Roles
Penetration testing is often confused with other cybersecurity roles, but it serves a very specific purpose. Here’s how it differs from other security-related tasks:
- Penetration Testers vs. Vulnerability Scanners: While penetration testers actively test systems by exploiting vulnerabilities, vulnerability scanners are automated tools that passively detect known weaknesses. Vulnerability scanners are useful for routine checks but cannot replicate the in-depth, manual attack simulations that pen testers provide.
- Penetration Testers vs. Security Auditors: Security auditors typically review security policies, procedures, and compliance standards within an organization. They ensure that companies are following security best practices and meeting regulatory requirements. In contrast, penetration testers focus on actively testing and exploiting technical vulnerabilities in an organization’s IT infrastructure.
- Penetration Testers vs. Incident Responders: Incident responders are experts who deal with security breaches after they’ve occurred. They investigate the attack, mitigate the damage, and develop strategies for preventing future breaches. Penetration testers, however, work proactively to identify weaknesses before an attack happens.
Why Are Penetration Testers Vital to Cybersecurity?
Penetration testers are crucial to an organization’s cybersecurity strategy for several reasons:
- Proactive Security: Rather than waiting for an attack to happen, penetration testers actively look for vulnerabilities and weaknesses in a system. By identifying these issues before hackers do, they give companies the chance to patch their security gaps.
- Realistic Attack Simulations: Penetration testers simulate real-world cyberattacks. This helps organizations understand how an attacker might exploit a vulnerability in practice, giving them insight into the real risks they face.
- Tailored Solutions: Unlike automated tools, which can only provide a generalized analysis, penetration testers provide tailored, actionable recommendations for improving a company’s security based on the specific vulnerabilities they’ve discovered.
- Compliance Assurance: Many industries have stringent regulations regarding cybersecurity (e.g., GDPR, PCI-DSS, HIPAA). Penetration testing helps ensure that organizations meet these compliance standards and avoid fines.
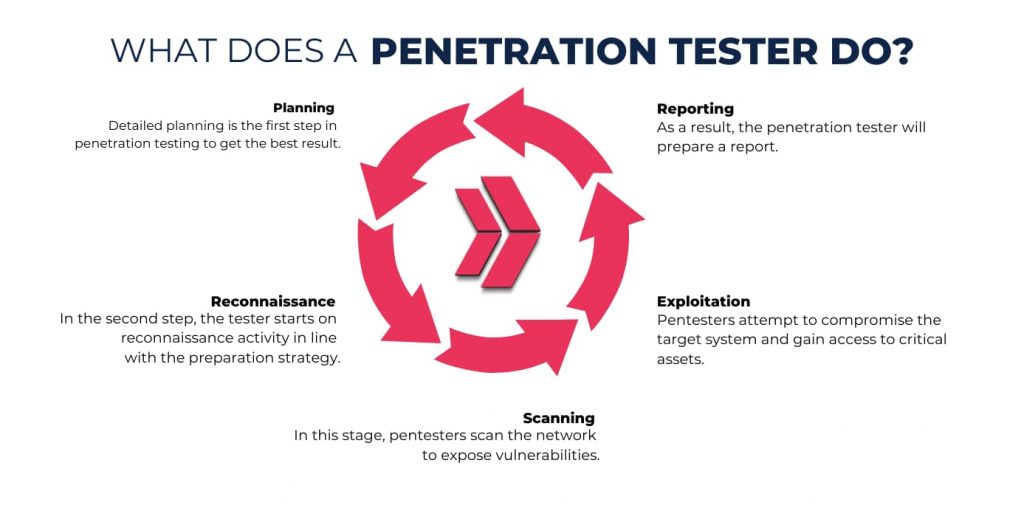
How Do Penetration Testers Work? The Step-by-Step Process
Penetration testing is a structured and methodical process that involves several key stages. Each stage is designed to mimic a real-world cyberattack as closely as possible, while also ensuring that it’s done ethically and within legal boundaries. Here, we’ll walk you through the typical steps of a penetration test, detailing what penetration testers do at each stage and why it matters for improving an organization’s security posture.
1. Planning and Scoping the Test
The first step in any penetration test is the planning and scoping phase. This is where the penetration tester and the organization collaborate to define the scope, goals, and boundaries of the test. Without a proper plan, a penetration test could miss critical vulnerabilities or end up unintentionally damaging systems.
Key Activities in the Planning Phase:
- Defining Objectives: The organization and pen tester determine what they want to test—whether it’s a web application, an internal network, or the security of a specific system.
- Understanding the Environment: Penetration testers need to understand the technology stack, including servers, applications, and software used by the company. This helps in tailoring the test to the specific environment.
- Agreeing on Scope: The scope of the test defines which systems, networks, or applications will be tested. It also specifies any excluded systems to prevent disruption of critical services.
- Setting Boundaries: Ethical hacking is all about staying within legal boundaries. Penetration testers and the organization will agree on the rules of engagement, such as the time and manner in which the test is performed. For example, tests should be conducted during non-peak hours to minimize disruption.
Why This Phase Matters:
- Permissions: Ensuring that all systems being tested are authorized by the company helps prevent any legal or ethical issues.
- Focus: Defining the test’s objectives and scope ensures the penetration test targets the most important assets, rather than testing everything without a strategic focus.
2. Information Gathering (Reconnaissance)
In this stage, penetration testers begin collecting as much information as possible about the target systems. This reconnaissance phase is typically divided into two types:
- Passive Reconnaissance: This type involves gathering information without directly interacting with the target systems. Pen testers might search publicly available sources, such as social media, domain registration records (WHOIS), or the company’s website, to collect information.
- Active Reconnaissance: In this step, pen testers actively probe the network and systems to uncover details like open ports, active services, and software versions. Tools such as Nmap and Nikto are used for this purpose. This type of reconnaissance is more intrusive but still happens without exploiting any vulnerabilities—at least not yet.
Key Tools Used in Reconnaissance:
- Nmap: A network scanning tool that allows testers to discover active hosts and open ports.
- WHOIS: A query tool that helps identify domain ownership, registrar information, and infrastructure details.
- Google Dorking: Using advanced search operators on Google to uncover sensitive information that may have been mistakenly exposed (e.g., login portals, exposed databases).
Why This Phase Matters:
- Strategic Advantage: Gathering intelligence on the target helps pen testers understand the network topology and identify potential attack vectors (e.g., outdated software, unprotected services).
- Reduced Risk of Detection: Passive reconnaissance allows testers to gather information without triggering security alarms or alerting the target company.
3. Vulnerability Scanning and Analysis
Once the information has been gathered, penetration testers move on to identifying potential vulnerabilities in the systems. This phase involves running automated vulnerability scanners and performing manual analysis to uncover weaknesses that attackers could exploit.
Key Activities in Vulnerability Scanning:
- Automated Scanning: Pen testers use specialized tools to scan the systems for known vulnerabilities. Tools like Nessus, OpenVAS, and Burp Suite automatically check for weaknesses like unpatched software or misconfigured services.
- Manual Testing: After automated scans, pen testers perform manual testing to confirm the vulnerabilities and ensure they haven’t been missed. This is especially important for more complex vulnerabilities like SQL injection or cross-site scripting (XSS) that automated scanners may not always catch.
Key Tools Used in Vulnerability Scanning:
- Nessus: One of the most popular vulnerability scanners, Nessus can detect vulnerabilities in operating systems, applications, and network services.
- Burp Suite: A tool used for web application security testing, which includes scanning for XSS, SQL injections, and other common vulnerabilities.
- Nikto: A web server scanner that checks for vulnerabilities like outdated software, security misconfigurations, and potential exploits.
Why This Phase Matters:
- Finding Vulnerabilities: Vulnerability scanning helps pen testers identify areas of weakness that need to be addressed. By discovering issues early, organizations can fix them before attackers can exploit them.
- Accuracy: Automated tools are good for quickly finding common vulnerabilities, but manual testing ensures that more complex issues are properly identified and analyzed.
4. Exploitation of Vulnerabilities
The exploitation phase is when penetration testers attempt to actively exploit the vulnerabilities they have identified. In this phase, they try to gain unauthorized access to systems, escalate privileges, or move laterally across the network.
Key Activities in Exploitation:
- Exploiting Known Vulnerabilities: Pen testers use known techniques and tools to exploit identified vulnerabilities. For example, if a tester finds an SQL injection vulnerability, they might try to manipulate database queries to access sensitive data.
- Privilege Escalation: Once initial access is gained, testers attempt to escalate their privileges to higher levels of access, such as admin or root privileges, allowing them to control the system fully.
- Lateral Movement: After gaining access to one system, testers often attempt to move laterally within the network to see how far they can penetrate the organization’s infrastructure.
Key Tools Used for Exploitation:
- Metasploit: A framework for exploiting vulnerabilities and gaining access to compromised systems.
- Kali Linux: An operating system that contains a suite of tools designed for ethical hacking, including John the Ripper for password cracking, Netcat for remote access, and more.
Why This Phase Matters:
- Simulating Real Attacks: This phase is the most critical in mimicking how a real-world hacker would exploit weaknesses to gain access to sensitive information or disrupt operations.
- Proving Impact: Successfully exploiting vulnerabilities demonstrates to the organization just how serious the identified issues are and the potential damage they could cause.

5. Post-Exploitation and Persistence
Once a penetration tester successfully exploits a vulnerability, they move into the post-exploitation phase. This is where the tester simulates the actions an attacker would take after gaining access to a system. The goal is to determine the extent of access gained, assess the potential damage, and test how easily an attacker could maintain access to the system over time.
Key Activities in Post-Exploitation:
- Establishing Persistence: After gaining initial access, penetration testers will attempt to maintain control over the system. This can involve setting up backdoors, creating new user accounts with elevated privileges, or exploiting vulnerabilities to ensure that the attacker could return even after the initial access point is discovered and closed.
- Privilege Escalation: In many cases, an attacker needs to escalate privileges to gain administrative or root access, which allows them to control the system more effectively. Penetration testers will often perform additional steps, such as exploiting weak passwords or exploiting misconfigured security settings, to elevate their level of access.
- Lateral Movement: Pen testers don’t just stop at the compromised system. They often attempt to move laterally within the network, exploring other connected systems to understand the breadth of access a real-world attacker could achieve. This might include accessing sensitive data or critical systems that could cause significant damage if compromised.
- Data Extraction: Penetration testers will sometimes attempt to gather sensitive information, such as confidential files or user credentials, to demonstrate the potential damage an attacker could cause. While they don’t use this data maliciously, it highlights the severity of the vulnerabilities present in the environment.
Why This Phase Matters:
- Real-World Impact: The post-exploitation phase simulates the most dangerous aspects of a cyberattack—gaining persistence and moving laterally through the network. This is a crucial part of penetration testing, as it helps organizations understand the long-term risks associated with the vulnerabilities discovered in the previous stages.
- Insight into Damage Potential: By exploring what an attacker can do with the access they’ve gained, penetration testers provide organizations with concrete examples of the real damage a breach could cause. This could include data theft, system downtime, or the compromise of critical assets.
- Security Gaps: Identifying how an attacker could maintain control and escalate privileges provides a clear picture of where security gaps lie. These insights allow the organization to strengthen its defenses and patch vulnerabilities before an attacker can take similar actions.
6. Reporting and Recommendations
After completing the penetration testing process, the penetration tester moves into the final and most important phase: creating a detailed report. This report documents all the findings of the test, including vulnerabilities discovered, how they were exploited, and the level of access achieved. It also includes actionable recommendations for fixing the vulnerabilities.
Key Elements of a Penetration Testing Report:
- Executive Summary: This section provides a high-level overview of the test, focusing on key findings and the overall security posture of the organization. It’s designed for non-technical stakeholders, such as executives or managers, and highlights the critical risks identified.
- Technical Findings: This section dives into the specifics of the vulnerabilities found, including technical details on how each vulnerability was exploited. It may include:
- Screenshots of exploited vulnerabilities
- Descriptions of attack methods used (e.g., SQL injection, cross-site scripting)
- A timeline of the attack process
- Risk Assessment: Penetration testers will assign risk ratings (e.g., critical, high, medium, low) to each identified vulnerability based on its severity and potential impact. This helps organizations prioritize which issues need to be addressed first.
- Mitigation Recommendations: After documenting the vulnerabilities and risks, penetration testers will provide actionable recommendations to fix the identified issues. This could include patching software, implementing more robust authentication measures, reconfiguring firewalls, or even conducting employee training to prevent social engineering attacks.
- Remediation Verification: In some cases, the penetration tester may also conduct follow-up tests to verify that the vulnerabilities have been properly fixed and that security improvements have been made.
Why This Phase Matters:
- Clear Communication: The report serves as the primary tool for communicating findings and solutions to the organization. It helps both technical and non-technical stakeholders understand the vulnerabilities and the actions needed to mitigate them.
- Risk Mitigation: The penetration testing report empowers organizations to take immediate action based on the findings, minimizing the likelihood of a real-world cyberattack succeeding. The risk assessment and mitigation recommendations are key to improving the overall security posture.
- Compliance: For organizations in regulated industries (e.g., healthcare, finance), the report may be used as part of their compliance efforts to demonstrate that they are actively addressing security risks and adhering to industry standards.
The step-by-step process of penetration testing demonstrates how professionals simulate real-world cyberattacks to uncover vulnerabilities and help organizations strengthen their security defenses. From planning and scoping the test to the final report and recommendations, each phase plays an integral role in identifying, exploiting, and ultimately fixing weaknesses in a company’s cybersecurity infrastructure.
Penetration testing is not just about finding flaws—it’s about improving security, ensuring compliance, and protecting organizations from the constantly evolving landscape of cyber threats.