Penetration testing, often referred to as “pentesting,” is a core element of modern cybersecurity. It involves simulating attacks on a computer system, network, or application to identify vulnerabilities before malicious hackers can exploit them. However, with the rapid advancement of technology and automation in the cybersecurity industry, one pressing question is being asked: Will pentesting disappear in the future?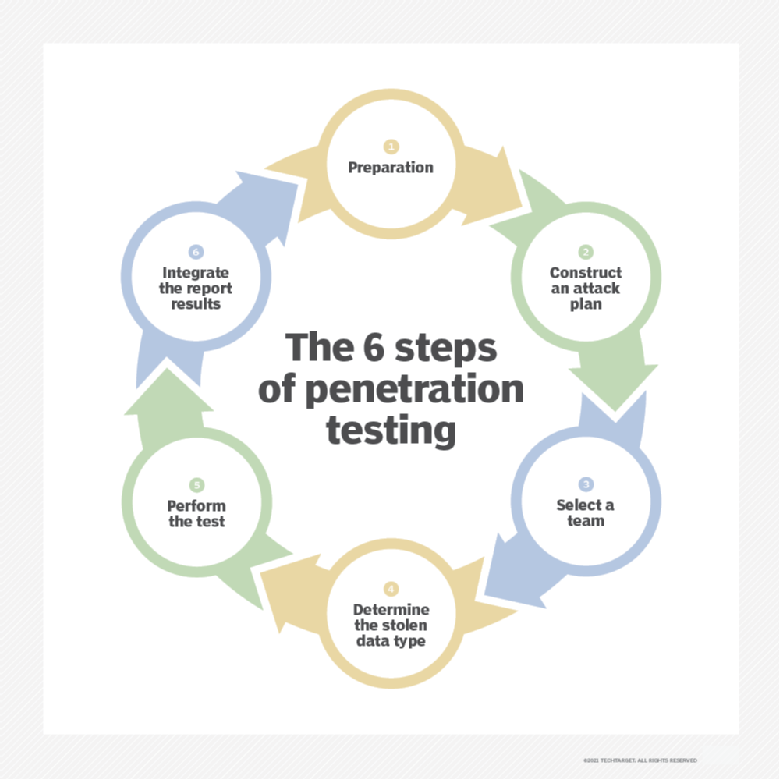
Penetration testing is a type of security testing where a cybersecurity professional, known as a “pentester,” tries to break into a system (like a website, network, or application) to identify any vulnerabilities. These vulnerabilities could be exploited by cybercriminals to gain unauthorized access or cause damage.
The main stages of a typical penetration test include:
- Reconnaissance: Gathering information about the target system, such as IP addresses, software versions, and potential weak points.
- Vulnerability Analysis: Identifying weaknesses, such as outdated software, unpatched systems, or misconfigurations.
- Exploitation: Attempting to exploit the vulnerabilities found to see how far an attacker could penetrate the system.
- Post-Exploitation: Analyzing what an attacker could do once inside the system (e.g., accessing sensitive data, deploying malware).
- Reporting: Documenting the findings and recommending steps for remediation.
Pentesting is critical because it helps organizations stay ahead of cybercriminals by proactively identifying vulnerabilities before attackers can exploit them.
The Role of Pentesting in Cybersecurity
Pentesting plays a vital role in proactive security. Rather than waiting for an attack to happen, pentesters simulate real-world attack scenarios, enabling organizations to address security gaps before they are targeted by hackers. This proactive approach is especially important in today’s world, where cyberattacks are increasingly sophisticated and damaging.
Some key reasons why pentesting matters include:
- Identifying Vulnerabilities: Pentesters can find weaknesses that may be overlooked by automated scanners or internal security teams.
- Risk Assessment: By simulating a cyberattack, pentesters can help organizations understand the potential impact of a breach and assess their security posture.
- Regulatory Compliance: Many industries, such as finance and healthcare, require regular penetration tests to comply with security regulations (e.g., GDPR, HIPAA).
- Building Trust: A successful pentest demonstrates to clients, partners, and customers that an organization takes security seriously and is committed to protecting sensitive data.
Real-World Examples
Several high-profile security breaches have occurred because vulnerabilities went unnoticed or were discovered too late. For instance, the 2017 Equifax breach affected over 147 million people and was largely due to unpatched software vulnerabilities that could have been identified through pentesting. Had Equifax conducted regular pentests, they might have spotted and fixed these vulnerabilities before hackers could exploit them.
Similarly, the Target data breach in 2013, which exposed the credit card information of millions of customers, could have been avoided with a more thorough penetration testing process to identify weaknesses in Target’s vendor management system.
As we see from these examples, pentesting is a key measure in identifying and addressing security gaps, helping businesses avoid costly breaches and data loss.

The Rise of Automation and AI in Cybersecurity: Threat to Pentesting?
As automation and artificial intelligence (AI) continue to shape various industries, the cybersecurity landscape is no exception. The integration of these technologies into cybersecurity tools has raised questions about the future of traditional pentesting. Can automated tools and AI replace human pentesters? Will pentesting disappear as more intelligent systems take over?
Can Automation Replace Human Pentesters?
Automation in cybersecurity has made significant strides over the last decade. Today, there are various tools that can scan networks, identify vulnerabilities, and even run basic attack simulations. These tools are particularly valuable for detecting common security issues, such as:
- Unpatched software vulnerabilities
- Weak passwords
- Misconfigured security settings
- Open ports and exposed services
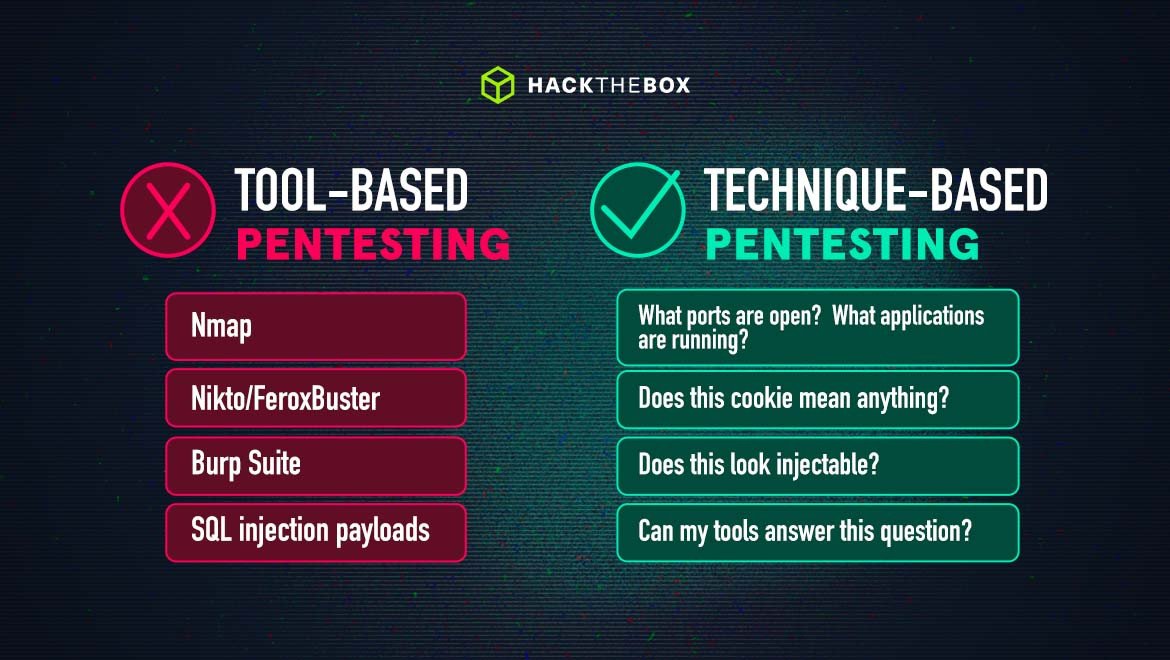
Automated tools are fast and efficient, making them an attractive option for organizations looking to perform routine security checks. However, automation cannot completely replace the role of human pentesters for several reasons:
- Complexity and Depth of Attacks: While automation can catch many common vulnerabilities, human pentesters excel at identifying complex and subtle security flaws. For example, many automated tools fail to identify vulnerabilities that require a more nuanced understanding of the system architecture, business logic, or real-world attack vectors.
- Manual Exploitation: Automated tools can scan for vulnerabilities, but they may not be able to fully simulate the exploitation of these vulnerabilities in the same way a human attacker would. For example, social engineering attacks (phishing, baiting) or physical penetration tests require human interaction, creativity, and judgment.
- Context and Strategy: Humans are adept at understanding the broader context of a system and adjusting their testing strategy accordingly. Automated tools may miss out on strategic exploitation, especially when systems involve intricate or custom configurations.
In essence, automated pentesting tools serve as a complementary asset to human pentesters. These tools can assist with routine scans, making the process faster and more efficient, but they cannot replicate the full range of skills and expertise a human pentester brings to the table.
The Role of AI and Machine Learning in Pentesting
AI and machine learning (ML) have started making their way into the cybersecurity space, promising to revolutionize the way vulnerabilities are detected and mitigated. AI and ML models can analyze vast amounts of data, identify patterns, and predict potential security risks with high speed and accuracy. For pentesting, this could mean:
- Automated Vulnerability Detection: AI can identify vulnerabilities based on patterns from historical data, helping pentesters find previously overlooked weaknesses.
- Predictive Threat Modeling: AI can assist in anticipating future cyberattacks by analyzing trends and patterns across different attack vectors.
- Intelligent Scanning: Machine learning can optimize vulnerability scanning by adapting to changes in the environment (e.g., newly added software, changed configurations) without needing manual intervention.
However, AI and ML technologies are still evolving, and there are several limitations that prevent them from fully replacing human pentesters:
- False Positives and False Negatives: AI systems, while powerful, are prone to errors. A model trained on a limited dataset may miss critical vulnerabilities or flag safe configurations as potential threats.
- Contextual Understanding: AI lacks the ability to understand the context of certain vulnerabilities or attacks. Human judgment is still required to assess the significance and potential impact of identified risks.
- Complex Attack Scenarios: AI and automated tools are generally less adept at simulating sophisticated attacks, such as multi-stage attacks or those involving social engineering. Human creativity and intuition are often necessary in these complex scenarios.
In short, AI and automation will enhance, but not replace, the role of pentesters. While these technologies will continue to improve and become more integrated into the pentesting workflow, they are not expected to make human pentesters obsolete.
Will Pentesting Disappear? 3 Key Factors to Consider
As we’ve seen, both automation and AI are transforming the way security testing is done, but the question remains: Will pentesting disappear? To answer this, we need to explore three key factors that will shape the future of pentesting: the evolution of cybersecurity threats, the need for human expertise, and the growing demand for pentesting skills.
The Evolution of Cybersecurity Threats
One of the most significant reasons pentesting will not disappear in the foreseeable future is the continuous evolution of cybersecurity threats. As technology advances, so too do the tactics used by cybercriminals. New vulnerabilities emerge, and old ones are exploited in novel ways. This dynamic landscape requires constant adaptation and testing to ensure security.
Growing Sophistication of Cyberattacks
Cybercriminals are becoming increasingly sophisticated. Attackers are no longer relying on basic exploits, such as SQL injections or phishing emails. They are now leveraging complex techniques, like advanced persistent threats (APTs), zero-day exploits, and multi-vector attacks that target different aspects of a system simultaneously. These sophisticated attacks often require deep knowledge of a target system and human intervention to understand and exploit specific vulnerabilities.
For example, in 2020, the SolarWinds cyberattack involved a supply chain compromise that was highly difficult to detect using traditional security measures. The attackers used a software update from the legitimate company SolarWinds to deploy malware into thousands of organizations, including U.S. government agencies and major private sector companies. This level of stealth and complexity would be difficult for automated tools to replicate or simulate without expert analysis.
The Rise of New Attack Vectors
With the proliferation of the Internet of Things (IoT), cloud computing, and AI-powered systems, new attack surfaces are constantly being created. These environments are often less secure, making them prime targets for exploitation. For example:
- IoT Devices: Vulnerabilities in connected devices (e.g., smart cameras, thermostats) are often overlooked by traditional security measures, yet these devices can be used as entry points for larger attacks.
- Cloud Infrastructure: While cloud platforms offer great flexibility, they also present challenges in terms of securing the complex configurations and shared responsibility models that cloud providers use.
- AI and Machine Learning Systems: The use of AI for automating decision-making also introduces new risks, such as adversarial attacks, where attackers manipulate the training data to make the AI behave in ways that benefit them.
Given the complexity and diversity of attack surfaces, pentesting will remain a crucial tool in identifying vulnerabilities across evolving technologies and attack vectors.
The Need for Human Expertise in Pentesting
Although automation and AI play an increasingly important role in cybersecurity, human expertise remains irreplaceable. There are several reasons why humans will continue to play a vital role in pentesting:
Creative Problem Solving and Strategy
Penetration testing isn’t just about running automated tools. It requires creative problem-solving, strategic thinking, and understanding the specific context of the organization being tested. Pentesters need to simulate how a real-world attacker would think and act, something that requires intuition and an understanding of social engineering tactics, business logic, and system interactions.
For example, a pentester may exploit a vulnerability in an overlooked API, or they may craft a phishing email to manipulate an employee into revealing sensitive information. These attacks require nuanced thinking and an understanding of human behavior, which automated systems cannot replicate.
Ethical and Legal Considerations
Penetration testing often requires navigating ethical and legal boundaries. Since pentesters are simulating attacks, they must be careful not to disrupt the organization’s operations or violate privacy. Human pentesters are required to:
- Follow ethical guidelines and professional standards.
- Ensure that tests do not damage systems or data.
- Handle sensitive data responsibly and within the bounds of regulations like GDPR or HIPAA.
These ethical considerations are a critical aspect of pentesting, and while automation can assist with scanning and identifying vulnerabilities, it cannot address the legal and ethical nuances involved in actual penetration testing.
Scenario-based Testing
Some attacks require testing scenarios that are complex, multi-layered, and evolve over time. For instance, pentesters may need to perform a red team exercise, where they simulate a long-term, covert attack on an organization’s infrastructure. This requires persistent, adaptive efforts that go beyond what automated tools can perform.
Growing Demand for Pentesting Skills in Cybersecurity
While there is no doubt that automation and AI are transforming cybersecurity, the demand for skilled pentesters is growing. As more organizations face the increasing threat of cyberattacks, the need for human expertise in pentesting is stronger than ever.
Job Market for Pentesters: Trends and Projections
According to the U.S. Bureau of Labor Statistics, cybersecurity jobs are expected to grow at a rate of 31% from 2019 to 2029, much faster than the average for other professions. Within cybersecurity, the role of ethical hackers and penetration testers is in high demand. As businesses and government organizations invest more heavily in cybersecurity, they are hiring skilled pentesters to stay ahead of attackers.
Specialized Roles in Cybersecurity
The rise of specialized security testing methods, such as red teaming and bug bounty programs, has further increased the demand for pentesting professionals. Red teaming involves simulating a full-scale attack on an organization’s security, not only focusing on technical vulnerabilities but also testing human defenses, physical security, and response protocols. Bug bounty programs, which involve rewarding ethical hackers for identifying vulnerabilities, are another growing area where pentesters play a vital role.
Pentesting Certifications and Skill Development
As cybersecurity becomes a critical priority for organizations, pentesters with specialized skills and certifications are highly sought after. Popular certifications for pentesters include:
- Certified Ethical Hacker (CEH): A certification that provides knowledge and skills in ethical hacking techniques.
- Offensive Security Certified Professional (OSCP): A widely respected certification for penetration testers focused on hands-on experience.
- GIAC Penetration Tester (GPEN): A certification that demonstrates expertise in penetration testing methodologies.
Pentesters are also expected to stay up-to-date with the latest tools, techniques, and vulnerabilities, which makes continuous learning and certification essential in staying competitive in the field.
Pentesting’s Future: Emerging Trends and Opportunities
As we’ve discussed, while pentesting may evolve with advancements in technology, it is unlikely to disappear. In fact, the future of pentesting looks more dynamic and integrated with emerging trends. These trends include red teaming, continuous security testing, and integration with other security measures, such as bug bounty programs and threat hunting. Let’s explore how these trends are shaping the future of pentesting.
Shift Towards Red Teaming and Continuous Security Testing
One of the most significant changes in the field of cybersecurity is the shift towards red teaming and continuous security testing. These methodologies represent a more comprehensive and ongoing approach to testing an organization’s defenses compared to traditional, one-time pentests.
Red Teaming: Beyond Traditional Pentesting
Red teaming is an advanced form of security testing that involves simulating the full spectrum of real-world attacks on an organization’s infrastructure. Unlike traditional pentesting, which focuses primarily on technical vulnerabilities, red teaming is more holistic. It encompasses not just network and system security but also physical security, human factors (social engineering), and organizational response protocols.
A red team will often operate covertly, without the knowledge of the organization’s internal security team, to simulate the tactics and methods of real-world cybercriminals. The goal is to test not only the technical defenses but also the organization’s ability to detect and respond to a persistent, sophisticated attack.
For example, a red team might attempt to gain physical access to a building, use social engineering techniques (like spear-phishing emails), and exploit technical vulnerabilities—all in an effort to breach an organization’s security. This type of comprehensive testing requires advanced expertise and strategic thinking, which is why it remains reliant on skilled human pentesters.
Continuous Security Testing: The Evolving Nature of Threats
In the past, many organizations would conduct pentests on a periodic basis—once every year or after significant infrastructure changes. However, given the growing sophistication of cyberattacks and the increasing pace of change in IT environments, continuous security testing is becoming a preferred approach.
With the rise of DevSecOps (development, security, and operations), organizations are embracing a more integrated approach to security. Rather than running a pentest as a one-time event, businesses are now incorporating continuous testing into their daily workflows. This approach leverages automated tools for ongoing vulnerability scans while integrating the insights from human pentesters to adapt and test emerging threats.
Continuous testing has several benefits:
- Faster identification of vulnerabilities as they arise.
- More adaptive response to changing threat landscapes.
- Ongoing compliance with security regulations, which often require regular testing and reporting.
Thus, pentesters of the future may focus less on occasional, one-off assessments and more on providing ongoing security testing and advice to keep systems secure in a constantly evolving digital world.
Integration with Other Security Measures (e.g., Threat Hunting, Bug Bounty Programs)
As the cybersecurity industry grows more complex, pentesting is no longer a standalone practice. It is increasingly integrated with other important security measures such as threat hunting and bug bounty programs. By working in tandem with these initiatives, pentesters can enhance an organization’s overall security posture.
Threat Hunting: Proactive Defense
Threat hunting involves actively searching for hidden threats within an organization’s network, rather than waiting for them to be detected by automated tools or discovered during an attack. It requires skilled professionals to identify anomalies, investigate suspicious activities, and neutralize threats before they can cause harm.
While automated tools can detect certain patterns of malicious activity, human threat hunters are still crucial for understanding the broader context and identifying more sophisticated or subtle threats. Pentesters and threat hunters often collaborate to ensure that an organization is not only protected from vulnerabilities but also resilient to active threats that may already be present within its systems.
For example, while a pentester might identify a vulnerability that could be exploited, a threat hunter would focus on identifying whether that vulnerability has already been targeted by attackers and whether any malicious activity is ongoing. This integrated approach strengthens an organization’s defense and response capabilities.
Bug Bounty Programs: Crowdsource Security
Another growing trend is the integration of bug bounty programs with traditional pentesting. A bug bounty program invites ethical hackers from around the world to search for vulnerabilities in a company’s software or systems in exchange for rewards.
While bug bounty programs do not replace traditional pentesting, they complement it by expanding the pool of talent searching for vulnerabilities. These programs often focus on specific types of vulnerabilities or software, while pentests typically cover broader security concerns.
Many organizations use both approaches simultaneously:
- Bug bounty programs provide continuous testing and encourage a wide variety of ethical hackers to explore systems.
- Pentesters provide deep, scenario-based testing, often simulating sophisticated attacks that go beyond what a typical bug bounty hunter might explore.
Together, these efforts ensure that vulnerabilities are identified from multiple angles, increasing the likelihood of finding weaknesses before they can be exploited.
The Future of Pentesting: Adaptation, Not Extinction
So, will pentesting disappear? The simple answer is no. While the practice of penetration testing will undoubtedly evolve, it remains a vital part of an organization’s cybersecurity strategy. Automation, AI, red teaming, continuous testing, and other emerging trends will enhance and supplement traditional pentesting, but they won’t replace it.
How Pentesting Will Evolve
Rather than disappearing, pentesting will likely undergo several important transformations:
- Greater integration with DevSecOps: Pentesters will work more closely with development and operations teams, providing continuous security testing throughout the development lifecycle.
- Specialized focus areas: As new technologies (e.g., IoT, AI, cloud computing) create new attack surfaces, pentesters may specialize in testing specific environments or threats.
- Ongoing learning and adaptation: Pentesters will need to stay current with new tools, techniques, and attack vectors in order to remain effective.
The Importance of Continuous Learning for Pentesters
To stay relevant in an evolving landscape, pentesters must focus on continuous learning. This includes pursuing certifications, attending conferences, and staying up-to-date with new tools and techniques. As cybersecurity threats become more sophisticated, so too must the skills of the pentester.
Some strategies to stay competitive include:
- Pursuing advanced certifications: such as OSCP (Offensive Security Certified Professional) and GPEN (GIAC Penetration Tester).
- Engaging in continuous training: Online platforms and labs (e.g., Hack The Box, TryHackMe) provide pentesters with hands-on experience in new tools and vulnerabilities.
- Networking with other professionals: Joining cybersecurity communities, both online and offline, to stay informed on the latest trends and share knowledge.